Cybersecurity Services
Proactive • Intelligent • 24/7 Protection for Modern Businesses
Cyber threats are increasing in complexity, frequency, and scale. Businesses of all sizes—from startups to enterprises—are prime targets for ransomware, phishing, data theft, and system compromise.
Wavestek provides end-to-end cybersecurity services powered by industry-leading tools and real-time threat intelligence. With best-in-class protection from CrowdStrike, Avanan, SonicSentry, FortiGate, SonicWALL, Datto, and more, we secure your data, devices, users, and cloud applications with a complete zero-trust approach.
Why Cybersecurity Matters Today
- Ransomware attacks can shut down operations in minutes
- Phishing is the #1 cause of corporate breaches
- Remote teams increase attack exposure
- Compliance requirements are getting stricter
- Data loss can permanently damage business trust
Wavestek delivers enterprise-level protection at every layer — network, cloud, endpoint, email, and identity.

Our Cybersecurity Services
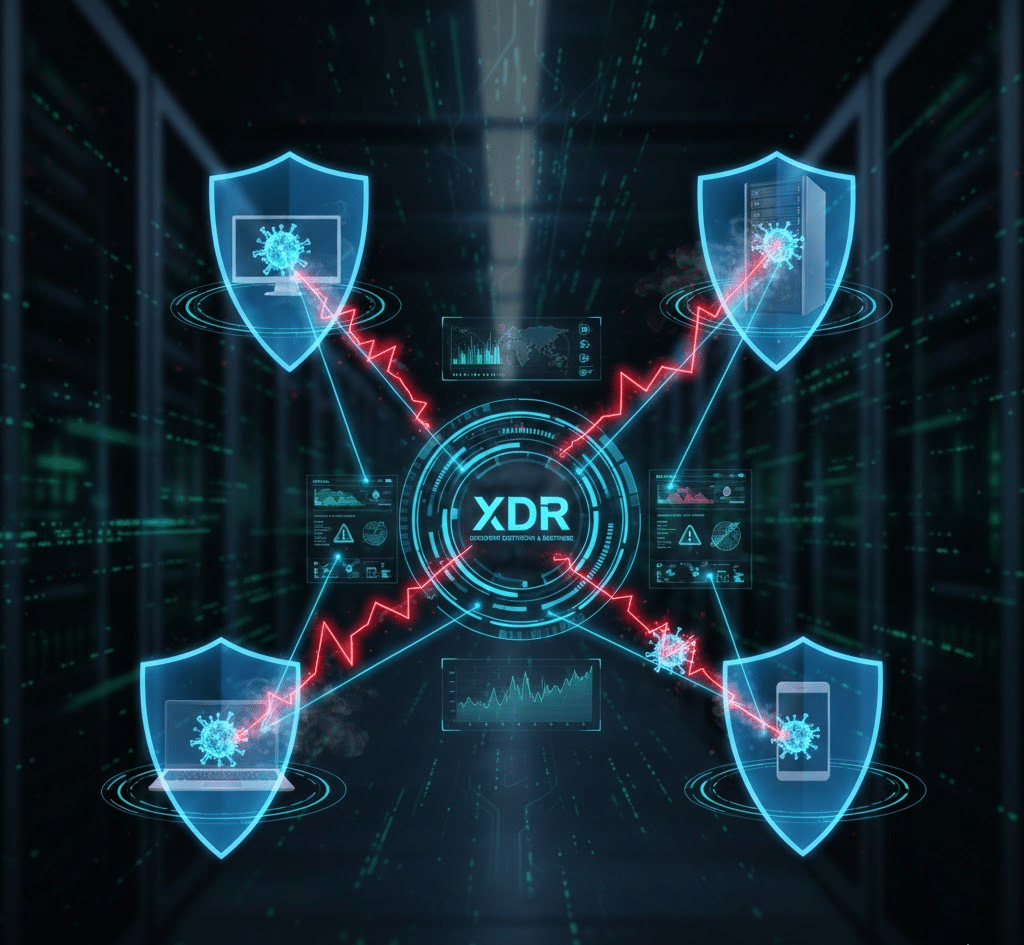
Endpoint Detection & Response (EDR/XDR)
Powered by CrowdStrike Falcon, the leading AI-based endpoint security platform.
- Threat detection & automated response
- Malware/ransomware prevention
- Device isolation during attacks
- Real-time monitoring
- Behavioral analytics
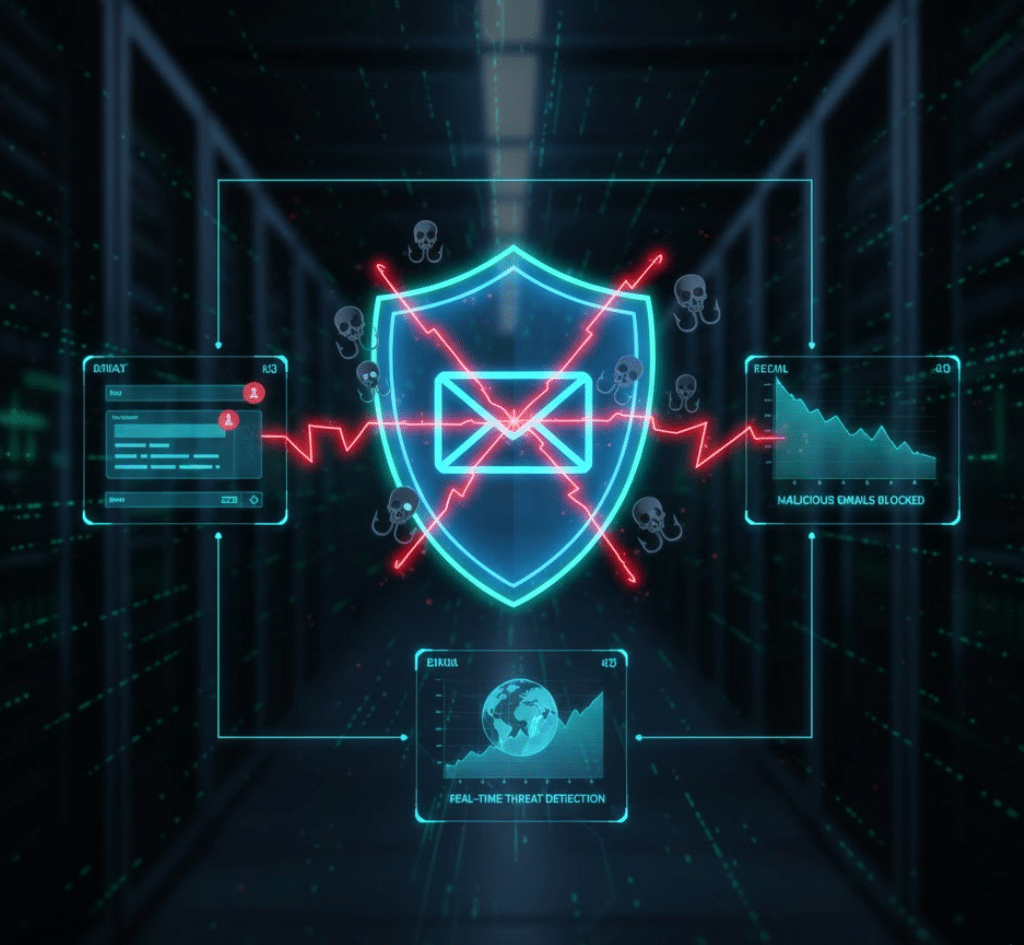
Email Security & Anti-Phishing Protection
- Advanced anti-phishing
- Business Email Compromise (BEC) prevention
- Attachment & URL sandboxing
- Suspicious login detection
- Cloud-native threat protection for M365 & Google Workspace
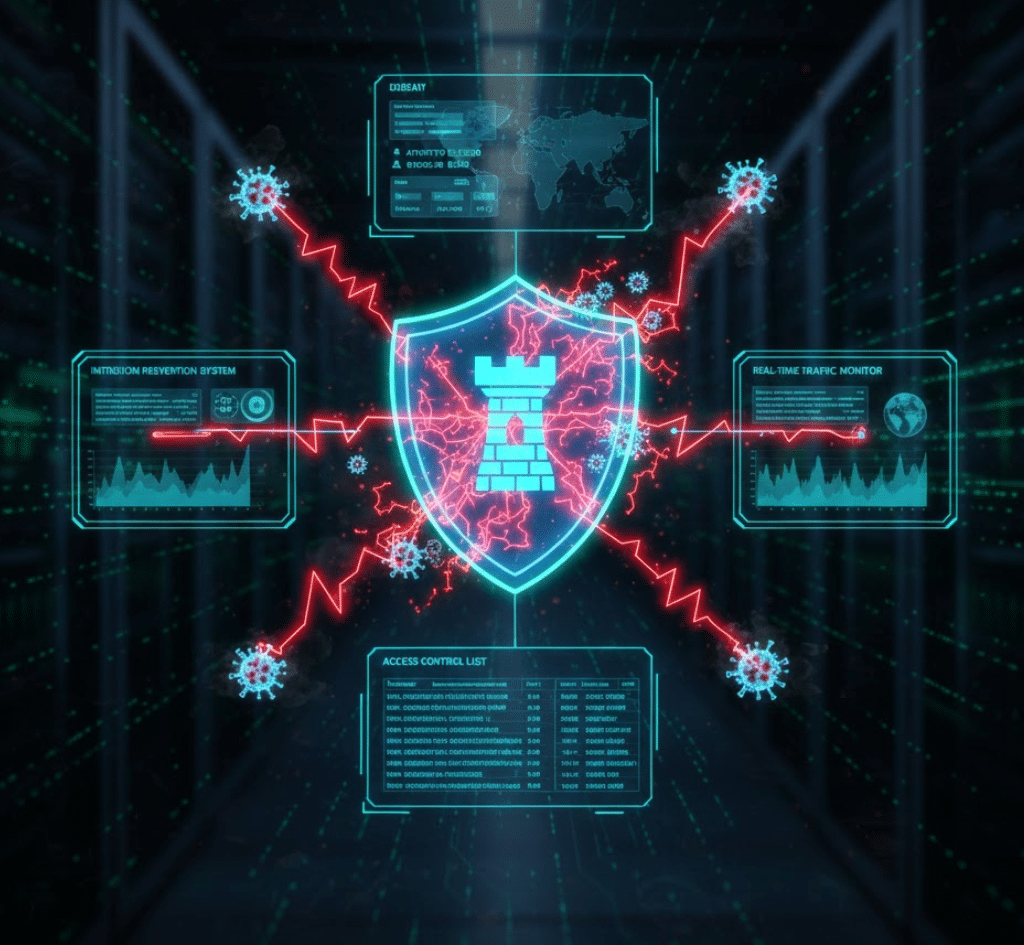
Network Security & Firewall Protection
Strong perimeter security with next-generation firewalls.
- SonicWALL
- FortiGate
- Palo Alto
- Sophos
- Firewall deployment & configuration
- Intrusion Prevention Systems (IPS)
- Web filtering & content control
- VPN setup for secure remote access
- Zero-trust network segmentation
Cloud Security
Protect your cloud assets on Microsoft 365, Azure, Google Workspace, AWS
- MFA & conditional access
- Identity protection policies
- DLP (Data Loss Prevention)
- Suspicious activity monitoring
- Cloud threat intelligence


Email & Data Backup Security
Powered by Datto, Synology, QNAP, and Veeam.
- Ransomware-resistant backups
- Immutable storage
- Cloud-to-cloud backup (M365/GWS)
- Automated daily backup monitoring
- Disaster recovery readiness
Vulnerability & Penetration Assessments
Identify weaknesses before attackers find them.
- Network vulnerability scanning
- Server & endpoint audits
- External attack surface review
- Penetration testing
- Security posture reporting

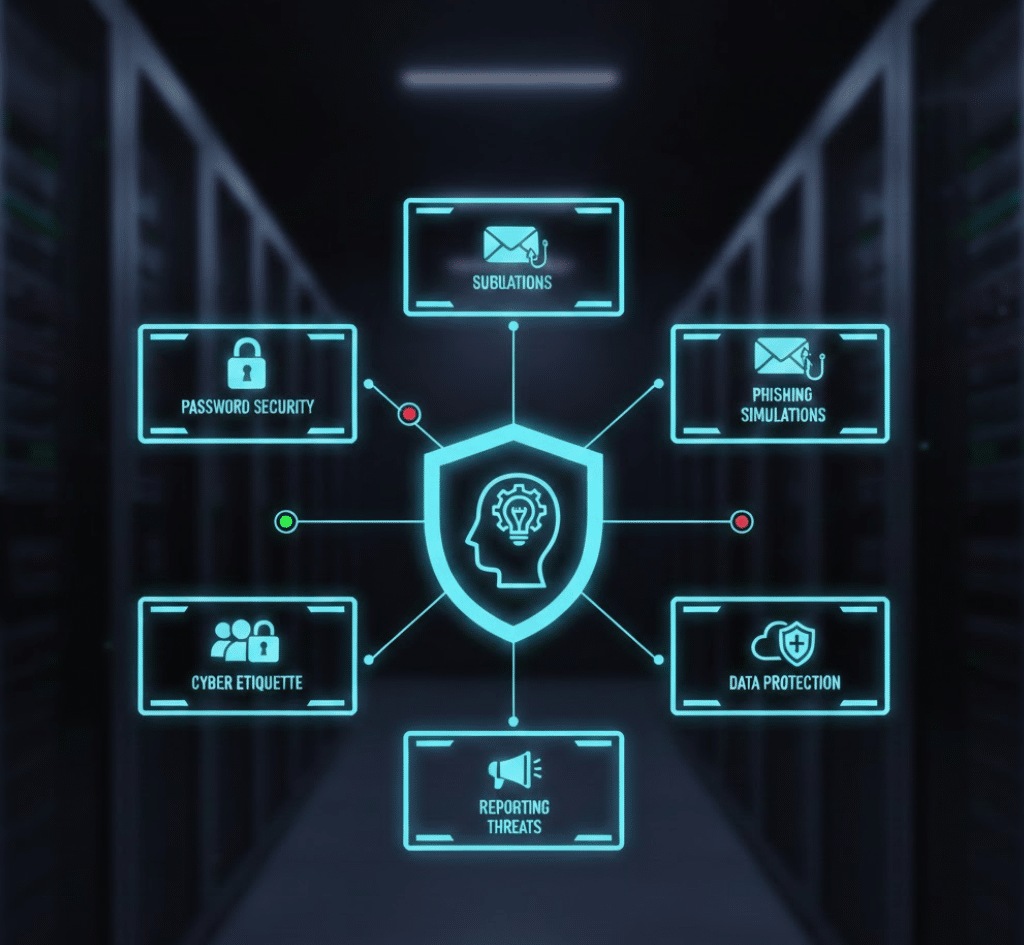
Security Awareness Training
Human error is still the biggest risk
- Phishing simulations
- Security workshops
- Monthly awareness tips
- Employee performance reports
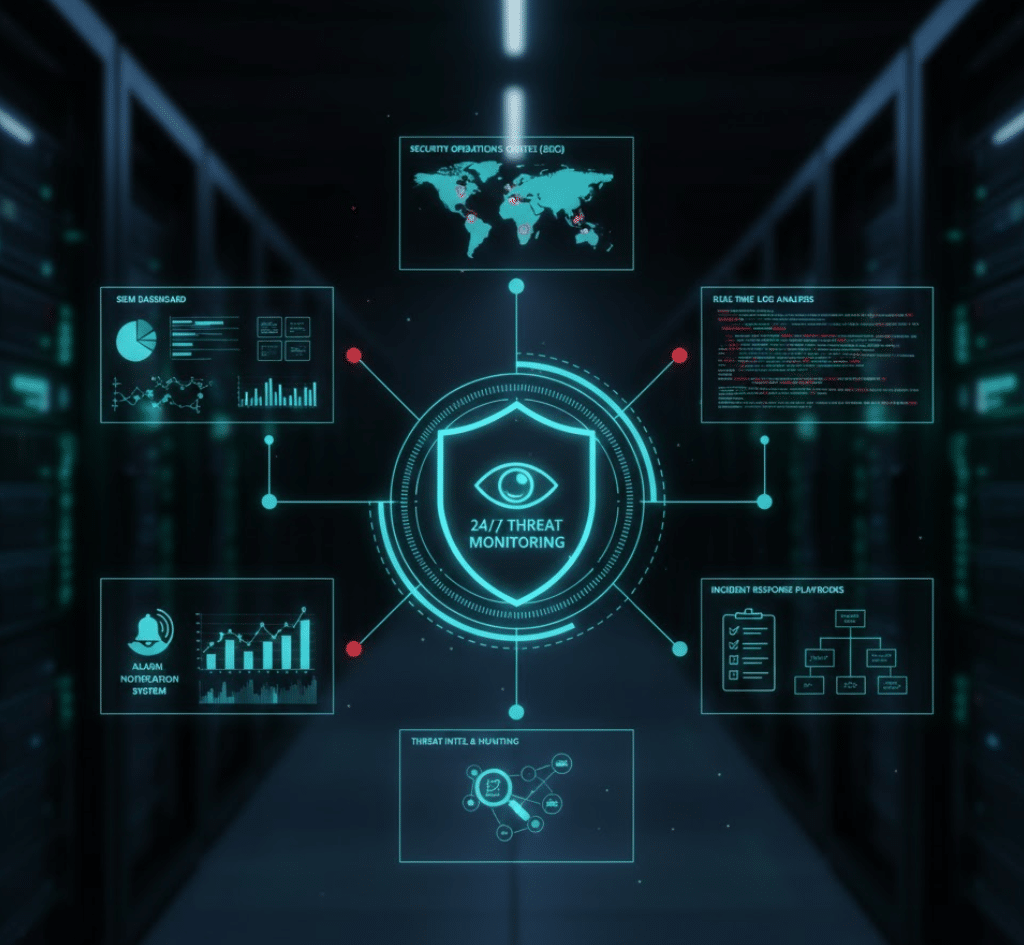
SOC & 24/7 Threat Monitoring
Round-the-clock security operations powered by AI + human expertise.
- Real-time threat response
- Log monitoring & SIEM integration
- Automated alerts
- Forensic analysis
- Incident response
(If you want, we can also add: “Backed by a 24/7 U.S.-based SOC team” — since you used this earlier.)
Our Technology Partners
(If you want, we can also add: “Backed by a 24/7 U.S.-based SOC team” — since you used this earlier.)
Endpoint & Device Security
- CrowdStrike Falcon
- Sophos Intercept X
- Microsoft Defender
Email & Cloud Application Security
- Avanan (Check Point)
- SonicSentry
- Microsoft Defender for M365
- Google Workspace Security
Firewall & Network Security
- SonicWALL
- FortiGate
- Palo Alto Networks
- Sophos Firewall
Backup & Ransomware Protection
- Datto
- Veeam
- Synology
- QNAP
Threat Intelligence & XDR
- CrowdStrike Falcon XDR
- Fortinet Security Fabric
- Microsoft Sentinel
Our Approach to Cybersecurity
Assessment & Security Gap Analysis
Risk Prioritization & Zero-Trust Design
Deployment of Security Layers (EDR, Email Security, Firewall, Backup)
Monitoring & Alert Response
User Training & Ongoing Hardening
Why Wavestek for Cybersecurity?
Powered by industry-leading tools
CrowdStrike, Avanan, SonicSentry, Datto
24/7 monitoring and rapid response
Experienced engineers with compliance expertise

Security-first approach in every deployment

Customized solutions for all business sizes
Transparent reporting & easy-to-understand alerts
Cyber threats evolve every day — your protection should too.
Let’s secure your business with enterprise-grade defense.